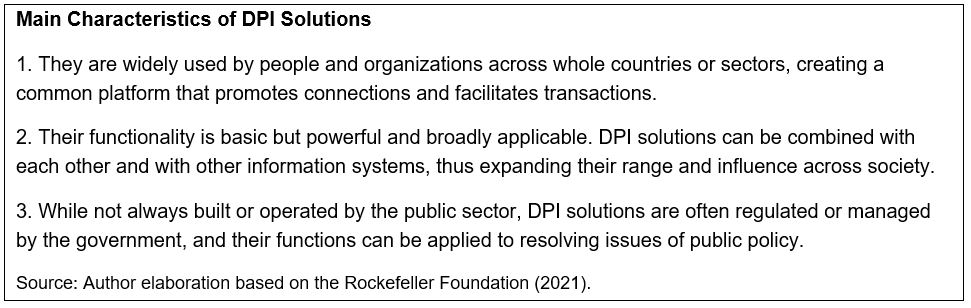
Countries around the world have been investing increasingly in Digital Public Infrastructure (DPI), particularly during and after the COVID-19 pandemic. These investments have the power to support the achievements of SDG, as well as eventually transform the management of public finances. But what is DPI? The Rockefeller Foundation (2021) defines DPI as digital solutions “that accomplish basic but widely useful functions and that can be used to build new applications for the greater good”. These solutions are generally developed in open-source platforms and have as an aim to support the achievements of the Sustainable Development Goals (SDGs). Such approach builds on recent initiatives to adopt digital solutions across the public sector - such as “government as a platform” and GovTech - and are related to the idea of a step-by-step modular approach to the development of digital solutions.
Broadly defined, DPI comprises interoperable digital “lego” blocks such as digital ID, data sharing solutions and payment systems. India has been leading the way on DPI applications. A well-known DPI solution called Aadhaar, India’s digital identity program, has successfully covered more than 1.3 billion people, providing citizens with greater access to social programs. In addition, India has adopted the vast Unified Payment Interface (UPI), an open protocol for instant money movement. In 2021, UPI processed around 39 billion transactions, totally US$940 billion, equivalent to 31 percent of India’s GDP.
However, the synergies and interactions between the digitalization of public finances and DPI concepts and applications have not yet been sufficiently explored. Based on a recent activities organized by FAD[1], the following issues related to the digitalization of public finances and DPI are as follows:
- Specific DPI initiatives for public finance need to be developed and piloted. The three core building blocks of DPI - digital ID, data sharing solutions and payment systems – are closely related to public finance, especially payment systems. But more work is needed on:
- Enhancing “fiscal” ID solutions that expedite the identification of taxpayers and the beneficiaries of government payments, grants, and transfers, thus helping to tackle evasion and corruption, among other issues.
- Developing a multi-dimensional classification of fiscal data that support the automatic sharing of information and improve the allocation, execution, and control of public expenditure.
- Adopting digital payment gateways and fintech payment applications for the public sector that improve their efficiency and transparency.
- Public sector institutional and technological capacities should be strengthened to adopt digital solutions based on the DPI approach. In many developing countries, IT systems related to public finance have structural weaknesses that could hamper the adoption of innovative digital solutions. For example, a country’s financial management information system (FMIS) may work in silos, hampering information exchange. Core FMIS functionalities and the system’s embedded controls are often flawed. Key processes such as procurement should be modernized to promote the participation of digital startups in the public sector.
- Cyber risks should be properly addressed while digital solutions are being developed. Cyberattacks and breaches of data privacy are emerging challenges that governments face in this digital age. For example, in April and May 2022 many of Costa Rica’s government agencies[2], including the finance ministry, suffered a ransomware[3] attack. The authorities managed to limit the damage, but this attack highlights the importance of governments adopting and implementing a cybersecurity strategy to manage the risks arising from digitalization initiatives.
[1] 2022 Annual Meetings / New Economy Forum panel on “Transforming Fiscal Policy Through Digital Public Infrastructure” as a well a workshop on DPI on August 2022.
[2] See more details at Costa Rica IMF Country Report No. 22/345, November 2022.
[3] A “ransomware attack” is a type of malicious software (malware) that threatens to publish or block access to data or a computer system, usually by encrypting it, until the victim pays a ransom fee to the attacker.




